Building automation has evolved from isolated technical systems into an integrated part of an organization’s digital infrastructure. As BMS and supervisory control systems are connected to IT systems, cloud platforms, and external vendors, entirely new requirements emerge for security in building automation.
This article provides a introduction to how modern security in building automation must be designed, why traditional approaches are no longer sufficient, and which principles form the basis for secure and future-ready BMS systems.
Security in Building Automation Has Shifted from Afterthought to Prerequisite
Today, building automation is part of the digital backbone of modern buildings. What were once standalone BMS systems on closed networks are now tightly integrated with IT systems, energy management, and cloud-based services. This development delivers major benefits in terms of operational efficiency and insight, but it has also introduced an entirely new threat landscape.
Security in building automation is no longer only about protecting technical installations. It is about securing data and maintaining stable operations. At the same time, unauthorized access must be prevented and trustin the systems preserved. As a result, security is no longer an optional add-on, but a fundamental prerequisite for modern building automation.

Why Security in Building Automation Is More Important Than Ever
Traditionally, security in building automation has relied on physical and network-based isolation. As long as the BMS operated on an internal network, it was generally considered secure. This so-called perimeter-based approach no longer works when buildings are connected to the internet and multiple vendors require access.
As a consequence, BMS and supervisory control systems are increasingly exposed to external networks. At the same time, they handle large volumes of valuable operational and building data. In addition, these systems control critical functions such as ventilation, heating, access control, and energy consumption, often to enable energy efficiency in commercial buildings. This makes them central to both operational continuity and security.
Building automation has therefore become part of what is commonly referred to as OT security (Operational Technology) and an attractive target for both targeted attacks and automated malware. As more systems, vendors, and users are interconnected, both complexity and attack surface increase.
A New Threat Landscape for BMS and Supervisory Systems
When building automation systems are connected to IT systems and cloud platforms, several new risk factors emerge. Vendor access often originates from unsecured endpoints, and passwords are frequently reused or lack sufficient complexity. At the same time, many systems are built on flat network architectures with insufficient segmentation.
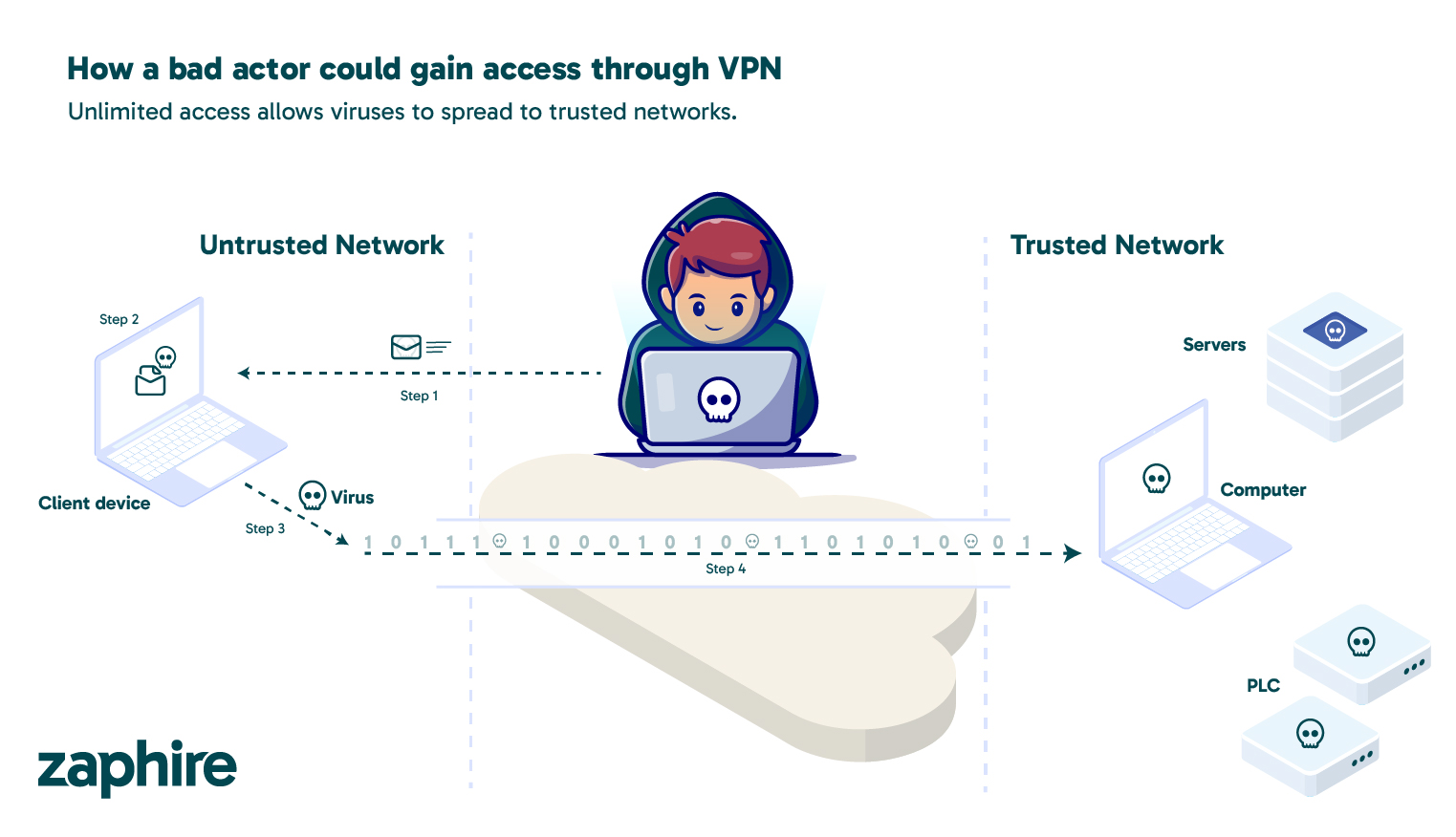
In addition, logging and traceability are often inadequate. This makes it difficult to detect and respond to unwanted incidents in a timely manner. In practice, this means that a compromised user device or a misconfigured VPN connection can give attackers far broader access than intended. Relying on trust within the internal network is therefore no longer sufficient. This threat landscape requires a security approach that goes beyond what traditional network models can provide.
Zero Trust - a Necessary Principle for Building Automation Security
As building automation becomes more tightly integrated with IT systems, cloud platforms, and external services, traditional security models have lost their effectiveness. In the past, systems located “inside” the network were assumed to be trustworthy, while threats were expected to come from the outside. This approach is no longer sufficient when BMS, supervisory systems, and sensors are accessible via the internet and multiple actors require access.
As a result, Zero Trust has become a core principle for modern building automation security. Zero Trust is also described by NIST as a key framework for modern IT and OT security.

What Does Zero Trust Mean in Building Automation?
In practice, Zero Trust means that no users, devices, or system components are automatically trusted, regardless of their location. In building automation, this means that neither the cloud platform, the local system, nor the user’s device assumes trust by default. All access must be explicitly verified, and trust is continuously evaluated based on identity, role, and context.
For BMS systems, this represents a clear departure from earlier practices, where access was often based on network location or physical presence. With Zero Trust, security shifts from the network layer to the application and identity layer, providing far better control over who has access to which functions, and when.
Continuous Verification and Encrypted Communication
A core element of Zero Trust in building automation is continuous verification of all communication. Every request between building, cloud, and user is validated, authenticated, and authorized before being processed. This applies not only to external users, but also to internal system components and services communicating with one another.
All data traffic is encrypted end-to-end, preventing interception or manipulation in transit. Even communication between internal microservices within the cloud platform is protected by dedicated security mechanisms, preventing a potential compromise from spreading further. The result is an architecture where security does not depend on a single barrier, but is embedded at every level.
For building owners and operators, this significantly reduces risk. Even if a user or device is compromised, the potential impact is limited and unauthorized access to the rest of the building automation system is prevented. Zero Trust thus becomes not just a theoretical model, but a practical and necessary foundation for modern building automation security.
For Zero Trust to work in practice, these principles must be embedded directly into the system architecture.
Secure Architecture from the Ground Up
Modern building automation security cannot be added as an afterthought. It must be an integral part of the architecture. How the platform is built, and how buildings communicate with the cloud, is critical to both security and operational stability.
Cloud-Based Building Automation Requires a New Security Mindset
Zaphire is not a traditional BMS that has later been adapted for the cloud. The platform is designed as a cloud-native solution, with security built into the foundation from the very first line of code. The entire architecture is designed to meet modern requirements for building automation security, including availability, scalability, and strict isolation between customers.
This aligns with Microsoft’s shared responsibility model for cloud security, where both the platform provider and the application owner have clearly defined and separate security responsibilities.
The solution runs on Microsoft Azure and uses a managed Kubernetes environment. This ensures high availability and redundancy, while allowing the system to scale automatically as needed. Each customer and each building is logically isolated, ensuring that data and services are never mixed across projects or organizations. For building owners, this results in a robust and stable platform that can withstand both technical failures and increased load without compromising security. The architecture also enables reuse of existing BMS systems without sacrificing security or control.
Closed Communication Between Building and Cloud
Communication between on-site IoT devices and the cloud platform takes place via a closed, outbound WebSocket connection over port 443 (HTTPS). All traffic is encrypted end-to-end and restricted to a clearly defined API, ensuring that only expected and controlled communication is permitted. Connections are always initiated from the building to the cloud, never the other way around.
As a result, no inbound ports are opened to the building, and there is no direct attack surface from the internet to local devices. This significantly reduces the risk of intrusion and is a key measure for achieving high security in building automation, even in complex environments.
For building owners, this means there is no direct technical path from the internet into the BMS, even though the system is cloud-connected.
Network Security Without VPN
VPNs have long been the standard solution for remote access to technical systems. In practice, VPNs often provide broad network-level access, significantly increasing risk if a single user or device is compromised.
Zaphire has therefore chosen not to use VPNs for vendor or user access. Instead, all communication takes place through the application layer via secure APIs. Users are never granted network-level access to buildings. All access is limited to a single, defined session and endpoint, and lateral movement between systems or buildings through the portal is not possible. Even if a user device is compromised, access remains strictly limitedand potential damage is contained.
Read more: Why Zaphire does not use VPN for vendor access
The result is a solution that follows the principles of segmentation and least privilege, where users are granted only the minimum access required to perform a task. Even with secure architecture and access models in place, users remain a critical part of the overall security picture. At the same time, this approach enables high flexibility in BMS systems without compromising security.
User Security, Authentication, and Traceability
Many security incidents in building automation are caused not by sophisticated attacks, but by human error. Incorrect password usage, insufficient access control, or unintended configuration changes are among the most common causes. For this reason, strong authentication and clear access management are essential.
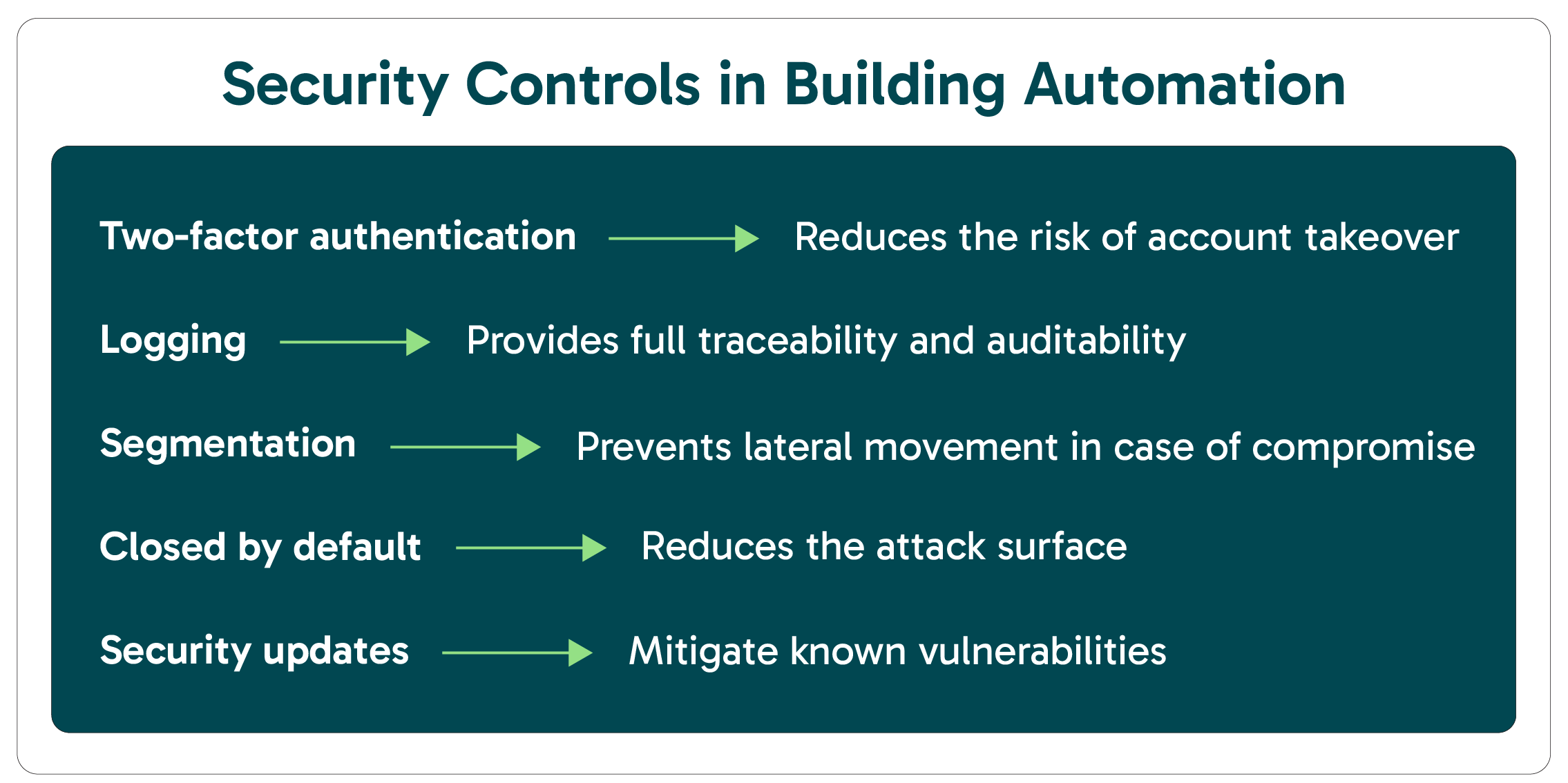
Zaphire supports this through strict password requirements and modern authentication mechanisms. The platform supports two-factor authentication via SMS or authentication apps, ensuring that login is based not only on something the user knows, but also something the user has. In addition, OpenID Connect is used for authentication, either through Zaphire’s own solution or integrated with the customer’s identity platform, such as Azure AD. This allows users to follow established organizational security policies within the building automation system.
All activity within the system is continuously logged. Every action is linked to a specific user identity, timestamped, and documented with details of the changes made. This provides full traceability and enables effective investigation of incidents, whether for troubleshooting, auditing, or security purposes. Changes can also be reversed in a controlled manner when needed.
To protect credentials, passwords are never stored in plain text. Instead, salted hash values are used, ensuring that even developers and operations personnel cannot access users’ actual passwords. This is a fundamental but critical measure for maintaining trust and high security in building automation.
Operational Reliability and Continuous Protection
Security in building automation also depends on availability and stable operations. Zaphire has a documented uptime exceeding 99.99%, enabled by an architecture that allows maintenance and updates without downtime. All changes are validated through automated testing across multiple stages, and underlying systems are updated weekly to address known vulnerabilities.
If a component in the cloud platform fails, services are automatically moved to a new node. Should the cloud platform be subjected to a DDoS attack, buildings are not affected. Local control continues independently of external events.
Standards, Regulations, and “Secure by Default”
Zaphire is continuously evaluated against international standards and frameworks such as ISO 27001, IEC 62443, NIST 800-207 (Zero Trust), and the EU’s NIS2 Directive. This ensures that building automation security is not only technically robust, but also aligned with regulatory requirements for critical infrastructure.
The platform also follows the principle of “secure by default.” All functions and APIs must be explicitly enabled through access control. This approach significantly reduces the attack surface, provides full control over access rights, and minimizes the risk of misconfiguration in complex environments with many users and integrations.
Building Automation Security Requires a New Approach
Security in building automation can no longer be treated as an add-on or a compromise between availability and protection. As BMS systems become part of an organization’s digital infrastructure, security must be embedded in architecture, access control, and operations. This requires solutions designed for today’s threat landscape, not retrofitted later.
Zaphire is built with this philosophy at its core. By combining Zero Trust principles, closed and encrypted communication, application-based access without VPN, and strong user and access management, Zaphiredelivers a unified and future-ready platform for building automation. For owners, facility managers, and operators, this means greater control, reduced risk, and a solution that can withstand both technological evolution and increasingly stringent regulatory requirements. Zaphire makes building automation security an integral part of everyday operations, not an afterthought.


